LATAM Bajo Ataque
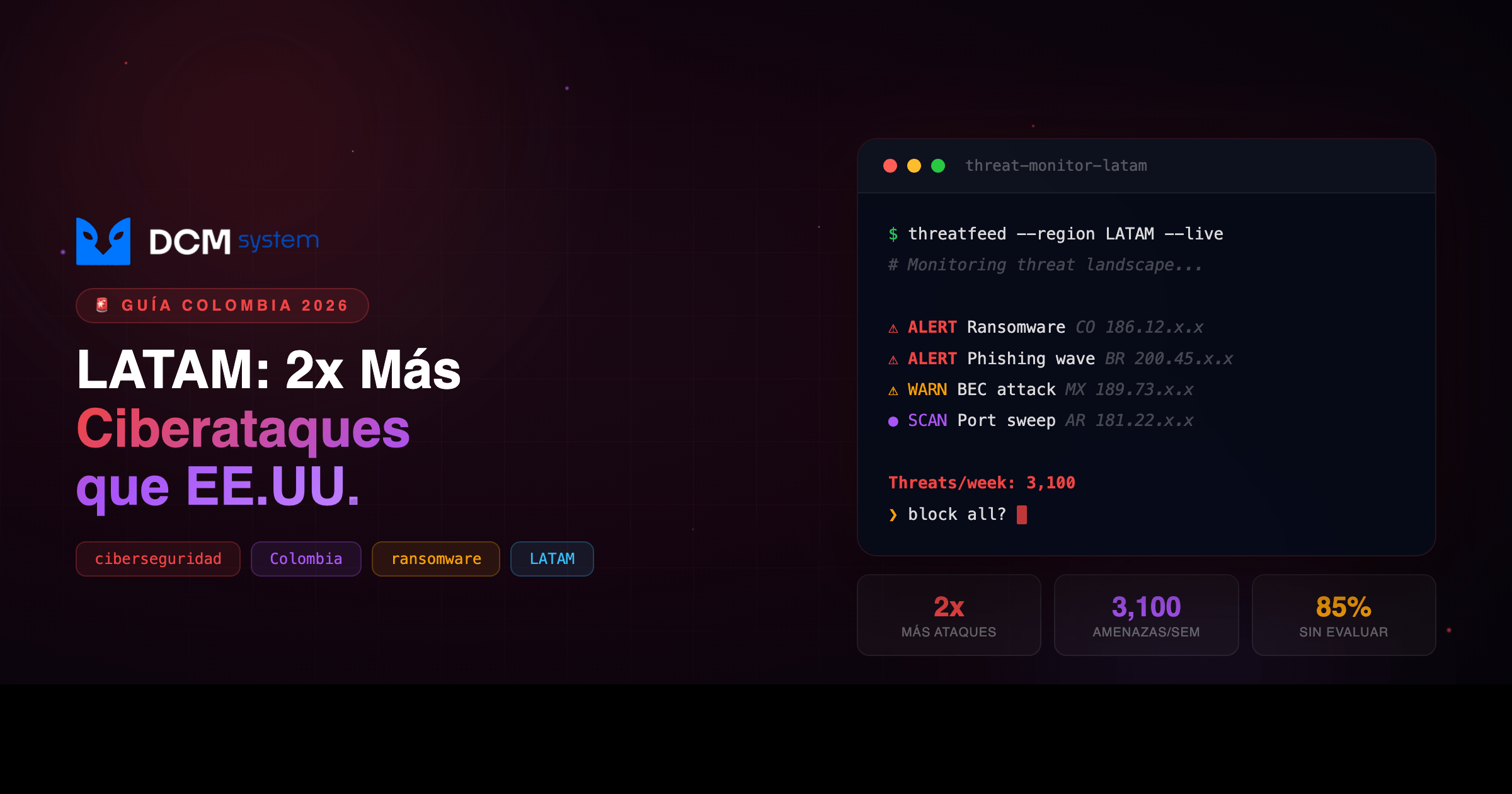
Las empresas colombianas reciben el doble de ciberataques que las de EE.UU. — con un tercio de la inversión en defensa.
[DATO REAL]: América Latina recibe 3,100 amenazas activas por semana y representa el 12% de los incidentes globales de IBM X-Force con solo el 4% de la inversión mundial en ciberseguridad. Fuente: IBM X-Force Threat Intelligence Index + WEF Global Cybersecurity Outlook 2026.
En este artículo vas a:
- Entender por qué Colombia es el 2.° o 3.° país más atacado de LATAM (con una economía mucho más pequeña que Brasil o México)
- Conocer los 5 vectores de ataque activos ahora mismo en empresas colombianas
- Saber exactamente qué te exige la ley colombiana — y qué le cuesta a tu empresa ignorarlo
- Armar un plan de defensa según tu presupuesto real, sin charlatanería
01 EL PROBLEMA REAL
Colombia es un blanco desproporcionado. No por el tamaño de su economía, sino por el desbalance entre los datos que manejan sus empresas y la inversión que hacen para protegerlos.
El World Economic Forum Global Cybersecurity Outlook 2026 lo dice sin rodeos: la brecha entre capacidad defensiva y volumen de ataques en LATAM se está ampliando, no cerrando. Cada año estamos peor en términos relativos.
Y el 85% de las empresas de la región no evalúan la seguridad de las herramientas de IA antes de implementarlas. ChatGPT, Copilot, automatizaciones en la nube — todo corriendo sin política de seguridad. Riesgo sobre riesgo.
Lo que falta no es tecnología. Es decisión.
PIÉNSALO ASÍ
Es como un banco sin alarma en un barrio con alta criminalidad. Las empresas colombianas manejan los mismos datos sensibles que las gringas — financieros, médicos, legales — pero con una fracción de la inversión en protección.
Antes de actuar El costo Después de actuar Blanco fácil, sin backups, sin plan Rescate de 50–500 MM COP Más difícil de atacar que el vecino
02 POR QUÉ PASA
Los atacantes operan con lógica de mercado. LATAM ofrece la combinación perfecta de datos valiosos con defensas débiles.
Transformación digital sin seguridad. La pandemia empujó a miles de empresas a digitalizarse en meses — e-commerce, pasarelas de pago, nube — y la seguridad quedó “para después”. Ese después nunca llegó.
Poca cultura de reporte. En EE.UU., un breach se reporta por obligación legal. Acá, la mayoría de incidentes se tapan o no se detectan. Los atacantes pueden vivir meses dentro de una red sin que nadie lo note.
Supply chain como puerta trasera. Las empresas grandes subcontratan a proveedores pequeños con cero seguridad. Comprometes al chico y tienes acceso al grande. Es el mismo vector de SolarWinds, pero mucho más fácil.
Ransomware como negocio escalable. Los grupos de ransomware descubrieron que las pymes latinoamericanas pagan. No tienen backups, no tienen plan, y un par de millones de pesos es nada comparado con una semana offline.
03 LA SOLUCIÓN
No hay un software mágico. Hay una decisión consciente de dejar de ser un blanco fácil.
Los atacantes siguen la ley del menor esfuerzo. Si tenés MFA, backups funcionales y un equipo que sabe identificar phishing, el atacante va a buscar al vecino que no tiene nada. No tenés que ser Fort Knox — tenés que ser más difícil que el de al lado.
Los 5 vectores activos en empresas colombianas ahora mismo:
1. Ransomware dirigido a pymes. Grupos como LockBit 3.0 y los sucesores de BlackCat tienen programas de afiliados. Cualquiera compra acceso a herramientas de ransomware y ataca pymes de 20–200 empleados. Entran por phishing o VPN desactualizada, se mueven lateralmente durante días, y cifran todo un viernes por la noche. El 60% paga porque no tiene backups funcionales.
2. Phishing con IA generativa. Ya no hay errores de ortografía ni príncipes nigerianos. Los correos son perfectos en español colombiano, imitando la DIAN, Bancolombia, la SIC. IBM X-Force reporta un aumento del 266% en uso de infostealers en LATAM distribuidos vía phishing.
3. Business Email Compromise (BEC). El favorito contra empresas con comercio exterior. El atacante compromete un correo en la cadena de comunicación y modifica datos de pago en una factura. La empresa paga al atacante. Casos documentados: USD 50,000 a USD 300,000 en una sola transacción.
4. Ataques a la cadena de suministro de software. Un atacante compromete una librería, un plugin, una API de proveedor pequeño — y entra a tu sistema. El vibe coding (apps generadas con IA sin revisar el código) está amplificando este vector brutalmente.
5. Credenciales y accesos expuestos. Contraseñas reutilizadas, RDP abierto a internet, bases de datos MongoDB sin autenticación, buckets S3 públicos con datos sensibles. Shodan muestra miles de servicios colombianos expuestos sin protección. La puerta abierta de par en par.
04 CÓMO IMPLEMENTARLO
El plan varía según presupuesto. No todas las empresas necesitan lo mismo — pero todas necesitan algo.
Nivel $ — Presupuesto mínimo (COP $2–5 MM/mes) — para pymes de 10–50 empleados:
- MFA en todo. Correo, VPN, paneles admin, cuentas bancarias. Google/Microsoft Authenticator son gratis. Bloquea el 99% de ataques por credenciales robadas.
- Backups 3-2-1 automatizados. Tres copias, dos medios, una offsite. Veeam Community Edition (gratis hasta 10 cargas) o Duplicati (open source). Testea la restauración cada mes — un backup no probado no es backup.
- Actualizaciones automáticas. Configura Windows Update, firmware de routers/firewalls, y parcha servidores en menos de 48h post-parche crítico. El 60% de los breaches explotan vulnerabilidades que ya tenían solución.
- Capacitación básica de phishing. Un taller trimestral de 2 horas. KnowBe4 tiene planes accesibles.
- Seguro de ciberriesgo. Desde COP $3 MM/año — Chubb, AIG, Sura tienen productos para el mercado colombiano.
Nivel $$ — Presupuesto intermedio (COP $10–25 MM/mes) — para 50–200 empleados o datos sensibles:
Todo lo anterior, más: firewall NGFW (FortiGate o Palo Alto), EDR (SentinelOne, CrowdStrike o Microsoft Defender for Business), pentesting semestral, monitoreo de logs con Wazuh o Elastic SIEM, y un plan de respuesta a incidentes documentado de 5–10 páginas.
Nivel $$$ — Presupuesto robusto (COP $50+ MM/mes) — para 200+ empleados o sectores regulados:
Todo lo anterior, más: SOC 24/7 (interno o MSSP), Zero Trust Architecture, programa de Bug Bounty o evaluación continua, DLP, y suscripción a inteligencia de amenazas (Recorded Future, Mandiant, o las alertas gratuitas del ColCERT).
05 ¿ES PARA TI?
Sí, si tu empresa:
- ✅ Maneja datos de clientes, proveedores o empleados (todos los mandan la Ley 1581)
- ✅ Tiene más de 10 personas con acceso a sistemas digitales
- ✅ Hace transacciones bancarias o comercio exterior en línea
No, si:
- ❌ Eres un freelancer sin empleados ni datos de terceros bajo tu responsabilidad
- ❌ Tus operaciones son 100% offline y no usas ningún servicio en la nube
El terreno legal: lo que te exigen
Esto no es opcional. Colombia tiene marco legal específico y la SIC ya está investigando y sancionando.
Ley 1273 de 2009 — Delitos informáticos. Penas de 4 a 8 años y multas de hasta 1,000 SMLMV por acceso abusivo, interceptación de datos o uso de malware. Si tu empresa sufre un breach por negligencia comprobada, enfrentas responsabilidad civil y administrativa.
Ley 1581 de 2012 — Habeas Data. Obliga a implementar medidas de seguridad “apropiadas” para datos personales. Un breach puede resultar en multas de la SIC de hasta 2,000 SMLMV — más de 2,600 millones de pesos en 2026.
Decreto 338 de 2022. Si le vendés software o servicios al gobierno, este decreto te aplica directamente.
Circular 007 de 2018 de la SFC. Sector financiero: framework de ciberseguridad formal, evaluaciones periódicas y pruebas de penetración obligatorias.
Preguntas frecuentes
¿Cuánto cuesta un ataque de ransomware real para una pyme colombiana? Entre 50 y 500 millones de pesos en rescate — sin contar el tiempo offline, la pérdida de clientes y la exposición legal. El costo total suele ser 3–5x el rescate pagado.
¿El ColCERT me ayuda si sufro un ataque? Sí, pero son un equipo pequeño y su capacidad de respuesta individual es limitada. Lo ideal es tener tu propio plan antes de necesitarlos. Sus alertas gratuitas sí son valiosas para inteligencia preventiva.
¿Los seguros de ciberriesgo realmente pagan? Sí, pero leen la letra menuda. La mayoría requiere que tengas controles básicos implementados. Si no tienes MFA activo al momento del breach, pueden negarles la reclamación.
Acción inmediata: Abrí Shodan (shodan.io) y buscá el nombre de tu empresa o tu rango de IPs. Si aparecen servicios expuestos que no sabías que eran públicos, ya sabés por dónde empezar.
¿Quieres ayuda? → Hablá con DCM — llevamos 12 años construyendo software seguro en Colombia y no nos da miedo decirte la verdad sobre el estado de tu seguridad.